Saturday, October 29, 2011
Facebook stops 600,000 suspicious log-ins a day
Sunday, October 23, 2011
Cloud storage

Why is cloud storage better than cloud computing? Because in some cases with cloud computing, if the server is down, my software is useless. But with cloud storage, as provided by Dropbox, the files are stored on a particular folder on my computer and after changes to one or more files in that folder are made, then my computer communicates with the central server to update its copies of those files. Once the server itself is updated, then it updates the folders on my other computer devices. But if the server goes down, I still have my files. This is a great medium through which to transfer raw data and files between devices and it doesn’t make me, the user, feel too worried about the server going down for an afternoon.
Sunday, October 16, 2011
Cloud computing

I think that cloud computing technology started to become popular and seen as an opportunity when individuals started spreading their computing across desktops, laptops, mobile phones, and tablets. All the software on these devices needed to communicate with each other so instead of making that happen companies decided to simplify it: instead of communicating with each other they will communicate with one central machine. In the cloud, instead of software being sold as a product, it is now sold as a service. The computing technology no longer lies with your machine but with the software company’s server. In a sense, we have regressed back to the original terminal-server setup. All of your eggs, will be in one basket, quite literally. The cloud is not a mysterious, omnipresent technological force. It’s a big machine in a big room. So what are the dangers here? In the words of Mark Twain, “If you put all your eggs into one basket, you better watch that basket!”
Next week we will look closer at cloud storage offered through Dropbox which I can definitely get behind.
Saturday, October 15, 2011
MIM Software
Saturday, October 8, 2011
The Evolution Of The Barcode... The RFID
The only reason RFID tags have not come full circle is because of how many different companies and sectors use barcodes. In the supply chain field, RFID has been implemented and makes distribution much more efficient. Now, tags are located on pallets and not individual products. The RFID scanners are used to track what leaves and enters the store or warehouse, where it's going/came from and at what time. This detailed information is sent to a system which records all data. As you can see this is much more efficient than scanning individual pallets and then entering information into a system because it is done for you and at a faster pace.
Here is an infographic featured in Baseline Magazine, of Wal-Mart and how they use RFID tags for their supply chain
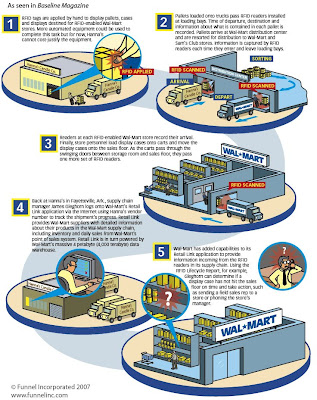
Source: HowStuffWorks & Funnel Inc.
The evolution of mobile phones
Hacktivists Part II
Misha Glenny says that there are observable character traits present in the majority of hackers he has met. Interestingly enough, most of them have Asperger’s syndrome, a mild form of autism. This manifests itself as highly specialized technical skill coupled with awkward social skills. In the life stories of the hackers he met, many of them developed their computer/hacking skills in their early to mid teens when their moral compass was still developing. Even Ryan Cleary, the hacker discussed in the last post, was diagnosed with Asperger’s shortly after his arrest in June. This information tells us that there are psychological and social reasons to explain the circumstances that create a hacker. Please keep in mind that very little, if any, scientific research has been done on the correlation between hackers and their psychological states. Furthermore, the goal here is not to pigeon-hole hackers but to try to understand the kinds of circumstances that might surround the decision to enter the field of cyber crime.
Now that we more fully understand the kinds of individuals we might be dealing with, we should ask, “Do we like hackers?” Are they totally scary? Do they represent a new kind of civil disobedience called hacktivism? Or both? They definitely are scary for several reasons: they are highly motivated, highly skilled, they exercise control over companies and governments seemingly without effort, and they remain hidden. If you can hack into the CIA and live to tell the tale without any jail time, then wow! You are damn good at what you do. The CIA, supposed masters of espionage, cannot pinpoint the identities of its hackers. Well, I’m not sure that a group like LulzSec could be described as engaging in hacktivism since they just do it for the laughs. On the other hand, Anonymous is more serious. We do have to hand it to them, they do tend to take down organizations we don’t like and also fear for other reasons. But you know, what do we really benefit from their schemes? I don’t know about you but I haven’t noticed any differences in my life because of them. I guess that’s what we need to ask ourselves. Are they actively changing the world for the better or just taking minor, ultimately insignificant, shots at the powers that be? We will see what the future holds in store for hacktivism.
Monday, October 3, 2011
Tyson Recalls Ground Beef After E. Coli Threat

On September 28th, Tyson Fresh Meats Inc. had to recall over 130,000 pounds of beef due to the discover of E. Coli within their product. This was detected first in Ohio because a family fell ill from eating the product. The ground beef was distributed to 6 different supermarkets among those were: Kroger and Food Lion. According to the USDA, the beef came from a Tyson plant in Kansas. This product through its different distribution channels reached several states, including Wisconsin, east to New York, south to Florida and west all the way back to Texas.
This presented such a huge health risk, with the founding report citing the child was hospitalized for 10 days. The interesting part to me is how Tyson was able to identify and trace all 131,300 pounds of beef that could have possibly been contaminated and the amount of detail. Obviously when working with such a big issue it is important to provide as much detail and information as possible to help come up with a solution. The only solution for a problem including contamination of a meat would be communicating the issue and notifying the affected party. Tyson along with the USDA was able to track the contaminated beef using UPC and product codes.
A list of retail stores has been created by the USDA:
Saturday, October 1, 2011
Hacktivists Part I
Well, who are we even talking about? If you haven’t already, meet the faces of cyber-insecurity:
Both are professional, worldwide hacking organizations. Both are very good at what they do. And both are very good at covering their tracks. What separates them is motivation. Anonymous is definitely more of a politically motivated group while LulzSec claims to do it just for entertainment value. They have hacked credit card companies, foreign governments, the FBI, the CIA, Sony Pictures, and the Sony PlayStation Network. In the battle between Chaos and Control, Chaos is winning, by a long shot. And if you don’t believe me then think of this, according to TIME magazine, cybersecurity incidents in U.S. government agencies have increased by 660% in the past five years. No that's not a typo, 660%. Not only that, some of these attacks came from foreign governments which I have no doubt were coordinated by their hired hackers. Needless to say, the threat is real.
That’s not to say law enforcement hasn’t made any headway. In June, 16 arrests were made nationwide for alleged members of Anonymous and in the same month Ryan Cleary, a 19-year-old with affiliations to LulzSec, was arrested as well. So what’s happened? LulzSec fled the scene! Despite asserting that Cleary’s participation was miniscule, LulzSec announced its retirement mere days after his arrest. In a tweet, they thanked their supporters and said, “The breeze is fresh and the sun is setting, so now we head for the horizon." We will see if their decision sticks or if it’s just a fake out. As for Anonymous, not much word from them, except for some current rumors that they will attack Facebook on November 5th. Why are they doing it? Cuz Facebook allegedly provided government agencies with personal account information. Again, we will have to wait and see what happens.
Stay tuned for Part II, where we will take a closer look at the individual hackers themselves, explore further the merits of hacktivism, and decide if hackers should be convicted or converted.
How BMW is dealing with an aging workforce
We all know that the world has advanced drastically over the last couple decades, and it has advanced even more in the technological factor. As more and more companies are seeking to become efficient and more productive, more and more jobs are going to robots since they can be programmed a certain way and produce the same product over and over in a fraction of the time. But that is not the case over at BMW, instead they are fearful of losing the craftsmanship and acquired skills of their older employees. Instead of forcing them to quit and bring in a much younger generation of workforce, BMW actually tweaked one of their assembly line to have an average worker age of 47 and then asked them what they would change to make it more comfortable for them. $50,000 and 70 small changes later, the assembly line saw an astonishing improvement in almost every factor.

